Barracuda Threat Spotlight AI-based protection helps to identify breached accounts and mitigate damage
Barracuda, a leading provider of cloud-first security solutions, has unveiled a new Threat Spotlight, that shows how attackers can misuse inbox rules in a successfully compromised account to evade detection while they – among other things – quietly move information out of the corporate network via the breached inbox. Not only this, but attacks can also ensure that the victims don’t see security warnings, file selected messages in obscure folders so the victim won’t easily find them or delete messages from the senior executive they are pretending to be in an attempt to extract money.
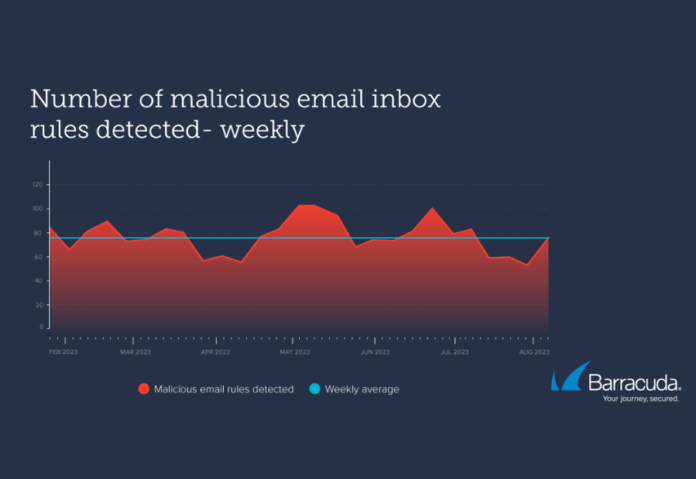
“The abuse of email inbox rules is a brilliantly effective attack tactic that provides stealth and is easy to implement once an attacker has compromised an account,” said Prebh Dev Singh, Manager, Email Protection Product Management at Barracuda. “Even though email detection has advanced over the years, and the use of machine learning has made it easier to spot suspicious rule creation – our detection numbers show that attackers continue to implement this technique with success. Malicious rule creation poses a serious threat to the integrity of an organization’s data and assets. Because it is a post-compromise technique, it’s a sign that that attackers are already in your network. Immediate action is required to get them out.”
Speaking on this issue, Parag Khurana, Country Manager, Barracuda Networks (India) Pvt Ltd, commented on the efficacy of this attack methodology: “The abuse of email inbox rules offers attackers both stealth and ease of execution once they compromise an account. In the Indian context, where cybersecurity challenges are constantly evolving, it is imperative that organizations adopt advanced defense measures and robust email security strategies to safeguard against threats. Barracuda remains committed to assisting Indian businesses in their cybersecurity journey, providing cutting-edge solutions to thwart attacks and protect data.”
The Clandestine Potential of Email Inbox Rules
Once an attacker successfully breaches a victim’s email account, they can create automated email rules to establish persistent access to the inbox. These rules can empower attackers to – Steal Information or Money: Attackers can configure rules to forward emails containing sensitive keywords like “payment” or “confidential” to external addresses, enabling them to purloin valuable information or funds while evading detection.
Conceal Inbound Emails: By relocating crucial inbound emails such as security alerts to obscure folders or erasing them, attackers can ensure victims remain oblivious to potential threats or command-and-control communications. Gather Intelligence: Attackers can surveil victims’ activities and amass intelligence on individuals and organizations, potentially for use in subsequent exploits or operations.
Facilitate Business Email Compromise (BEC): In the case of attacks on businesses, perpetrators may set rules to delete incoming emails from specific colleagues, enabling them to impersonate key figures like the CFO and deceive colleagues into transferring funds to accounts controlled by the attackers.
Notably, these malicious rules can persist even if the victim changes their password, activates multi-factor authentication, or imposes stringent access policies. As long as the rule remains undetected, it poses a substantial threat.
Effective Defense Measures Against Malicious Email Inbox Rules
Prevention remains the most effective protection against the exploitation of email inbox rules. Detecting and mitigating the repercussions of breached accounts necessitates comprehensive measures, including:
Comprehensive Visibility: Organizations need insight into every action occurring within employees’ inboxes, encompassing rule creation, modifications, logon history, email context, and more.
AI-Based Protection: Leveraging artificial intelligence, organizations can construct intelligent user profiles to discern subtle irregularities and promptly flag them for attention.
Impersonation Protection: Employing multiple signals, including login and email data, to pinpoint account takeover attempts.
Extended Detection and Response (XDR): Solutions such as Barracuda’s XDR Cloud Security, coupled with round-the-clock monitoring by a Security Operations Center (SOC), ensure that even deeply concealed and camouflaged activities are detected and neutralized.
Also read: Trends of the latest technologies
Do Follow: CIO News LinkedIn Account | CIO News Facebook | CIO News Youtube | CIO News Twitter
About us:
CIO News, a proprietary of Mercadeo, produces award-winning content and resources for IT leaders across any industry through print articles and recorded video interviews on topics in the technology sector such as Digital Transformation, Artificial Intelligence (AI), Machine Learning (ML), Cloud, Robotics, Cyber-security, Data, Analytics, SOC, SASE, among other technology topics.





